When OCS (or was it OCS 2007 R2?) first really featured enterprise voice and had deskphones, there were two types. One was the Tanjay, a futuristic, right angled obelisk of discomfort, and Aries.
Tanjay was interesting in that it would allow you to type your AD credentials on the touch screen, if you had the patience. It was a terrible interface for sure. More often than not, the USB “better together” over ethernet function was used. The receiver (the part you hold in your hand, for those that might not share this same terminology) was uncomfortable to hold in your hand, to press against your head, and to squish it between your head and should was agony. I screamed in terror when one customer advised me that they had found 50 of these units on sale on eBay or some other site for “cheap cheap cheap!”.
The Aries phone was less edgy (literally and figuratively), and the Polycom CX500 and CX600 series were perhaps the most deployed (and most loved) phones of the group. They worked well, felt comfortable, had enough features without being rocketships, and just worked.
Both Tanjay and Aries devices are part of Lync Phone Edition, or LPE, family of devices. The software for these devices was provided by Microsoft – as were some initial physical design – with the manufacture and support of the devices left to the manufacturer – Polycom, Aastra (since acquired by Mitel), and HP. I think it’s fair to say, however, that these devices were underspec and thus underpowered when it came to doing true enterprise level telephony. Specifically, the lack of ability to any soft of programming or customization, and the woeful response time for call setup in a response group.
Under the hood, the LPE devices ran Windows CE. Win CE (or wince, if you weren’t a fan) hasn’t been a desired or supported development platform for some time now. It doesn’t support TLS 1.2 and above, which means that it’s soon to be no longer supported with Office 365 (to be clear, this means “will no longer work” versus “don’t call us if something doesn’t work right, but it might be ok”), nor in most on-prem or hybrid environments with a basic understanding of the risks of running out-of-date security protocols like TLS 1.1.
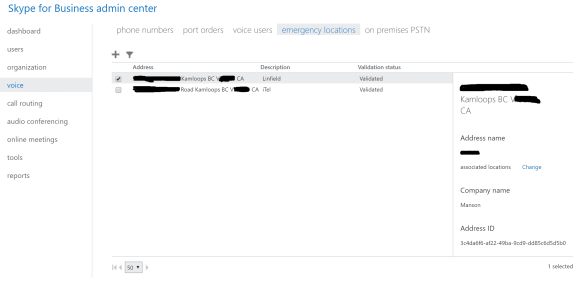
LPE devices were managed natively through Skype for Business. Initially, this was via a HORRIBLE nightmare of SharePoint team services ugliness, then directly supposed through later versions of Lync/SfB. I should clarify that by “Managed”, I mean chunky and clunky firmware update processes that were about as graceful as an elephant on figure skates. Reporting was iffy, and embarrassing, to be honest.
Rewinding a few years, we saw the introduction of 3PIP, or 3rd Party IP Phone, in late 2011 . These devices didn’t run the Microsoft provided Win CE software, or run the Microsoft dictated hardware under the hood. Instead, Microsoft provided a framework for IP Phone vendors to develop their own devices that would be certified to function with Lync and then Skype for Business. These devices offered a much increased level of customization, were faster, and with a number of different manufacturers producing a number of different models, 3PIP provided more than an adequate spectrum of devices for your telephony pleasure.
3PIP phones can mostly be managed the same as LPE devices, or instead you could (and should) manage them through the manufacturers management software. This approach can be hit and miss. For the ability to configure all kinds of functionality on the devices from a central platform, we give two thumbs up. For those who had to suffer with multiple vendors, and thus multiple management servers and differing feature sets, feature support, and ability to not hate your job, we are obliged to give two thumbs down, and more if we could.
With the introduction of MS Teams, we’re about to see the introduction of phones that again run Microsoft provided code, like the LPE, on vendor provided devices. The really interesting part here, is that the platform for this code is Android. Yup – the platform for “Microsoft Teams” phones is Android. Microsoft had indeed changed!
When it comes to Microsoft phone systems online, there may be some gotchas. First, LPE is soon to be out of the picture. It’s unrealistic to update the decade old software on the decade old hardware to support modern encryption and provide user experience that feels good and doesn’t involve smashing the device with a hammer.
Next up, let’s talk about 3PIP. The 3PIP devices all talk SIP, and work very well natively with Skype for Business – online and on-premises. When it comes to MS Teams support, you can expect basic phone functionality, but not much more than that. 3PIP devices run SIP, and MS Teams runs MNP24 with SIP for backward compatability. 3PIP devices are connecting to MS Teams through a gateway for Teams connectivity. There will be some MS Teams functions that will likely never reach these devices. Specifically, modern portal device management, media bypass (Teams, not SfB Server media bypass), and less mainstream calling features like call park/retrieve.
And now on to MS Teams devices. These are the future of the Microsoft phone product line, including desktop phones, conference room phones (“starfish”), and for some room system devices. I expect lots of feature growth here, including when beefier hardware is needed – this is just a Teams app running on Android, which is a much more agile platform than the legacy days of Win CE.
The moral of this post, is that you should avoid LPE devices at all costs, including for on-prem (how long until the OS/Skype for Business Server app no longer support that laughable “security” that TLS 1.1 and below provide?). 3PIP devices are great, but going forward I be cautious. While they’ll work with SfB and SfBO and MS Teams, the fact that they connect via a gateway to MS Teams and have limited MS Teams modern portal support means that some caution is warranted. Make sure that they’ll be able to do what you require in terms of functionality, but also management now and in the future.